Money laundering is a huge problem everywhere in the world. Unfortunately, while cryptocurrency means cheaper and faster international transactions, it also makes the crypto sector ripe for criminal activity, such as money laundering and the funding of terrorist organizations.
According to the AML directive from the FATF, all countries had to introduce into their legislation regulations regarding combating money laundering using cryptocurrencies in 2020. Following the directive, many companies resort to AML and KYC procedures.
Today, every person or firm planning to build a secure and legal crypto project, should be aware of these rules and comply with them.
Considering a number of different concerns related to the AML and KYC compliances, in this article we will figure out crucial points of the rules, why and how to implement them in blockchain projects, and give you few tips on how to save fortunes on compliance implementation.
What is KYC in Blockchain?
KYC (Know Your Customer or Know Your Client) is the principle of operation of financial institutions, which obliges them to identify the identity of a person before they can conduct transactions. This identification serves many purposes: understanding your clients, monitoring operations, reducing risks, fighting bribery and corruption. Examples of KYC procedures include limits on cash withdrawals from an account or verification of a client’s identity using a code from an SMS. Thanks to this principle, a financial institution determines who can become its client, and can also obtain basic data about the client, track and evaluate its transactions, and increase the security of these transactions.
The KYC procedure obliges all financial institutions, including cryptocurrency exchanges, to identify and verify the identity of every client. And this must be done before they can conduct financial transactions. KYC protects companies from the risk of dealing with fraudsters and terrorists and ensures the safety of customer assets. Once upon a time, KYC was only an internal policy of different companies. But for the past five years, KYC has established itself as a mandatory legal practice.
Crypto exchanges have the right to determine the stages of verification themselves, but the requirements for user data are as follows:
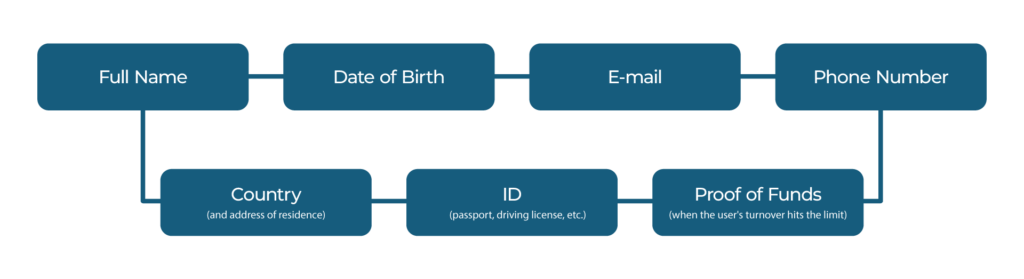
- Full name
- Date of Birth
- phone number
- country and address of residence
- ID (passport, driving license, etc.)
- proof of funds (when the user’s turnover hits the limit)
Simply providing data is not enough. A phone number must be confirmed with a one-time code via SMS. Other verification includes passport data such as photos of documents and selfies with them and residential addresses, for example, a utility bill.
How To Implement KYC Compliance
There are three components of KYC which include:
- Customer Identification Program (CIP). In order to comply with it, a financial institution should ask the customer for identifying information.
This information could include:
- A driver’s license
- A passport
For a company, this information could include:
- Certified articles of incorporation
- Government-issued business license
- Partnership agreement
- Trust instrument
- Customer Due Diligence (CDD). This component means requiring financial institutions to do further detailed risk assessments. Financial institutions examine the types of transactions a customer may make in order to detect anomalous behavior. After this, the institution can assign the customer a risk rating. Institutions have to verify the identity of any individual who owns 25% or more of a legal entity.
- Continuous monitoring. This means that financial institutions have to monitor their client’s transactions continuously for suspicious or unusual activity. When suspicious or anomalous activities are detected, the financial institution has to submit a Suspicious Activities Report (SAR) to FinCEN and other law enforcement agencies.
What is AML in Blockchain?
Officially, the concept of AML was established after the creation of the FATF (Financial Action Task Force on Money Laundering) back in 1989. The full version of the title refers to Anti-Money Laundering, Combating the Financing of Terrorism and Financing the Development of Weapons of Mass Destruction.
So what do crypto exchanges have to do with it? The transparency of a blockchain network relies on the ability of users to track the history of any transaction in a cryptocurrency. Despite the fact that this information is in the public domain, it does not allow for identifying the owners of crypto wallets or revealing reasons for transferring funds. But any transaction can be associated with illegal activities such as terrorism, phishing, or ransom. Like many other great developments, crypto is not protected from use for criminal purposes. Therefore, when buying a cryptocurrency “from hands”, we will never know whether these hands were “clean”.
To identify funds obtained through criminal means, the AML policy is being implemented on crypto exchanges. It includes a wider set of measures than KYC:
- transaction monitoring
- checking crypto for purity (crypto-compliance)
- risk assessment
- verification of bank cards, etc.
In short, crypto exchanges are doing everything to ensure that not even a single cent that has been stolen or used in criminal activities reaches our wallets.
What is the Travel Rule?
The Financial Action Task Force on Money Laundering, the intergovernmental organization that develops anti-money laundering (AML) policies for the G7 and about 30 other rich countries, issued FATF Recommendation No. 16, also known as the Travel Rule, to combat heightened concerns about money laundering in the crypto market.
The travel rule requires organizations to collect and share the personal data of parties to a transaction. Initially, the rule only applied to banks. However, in 2019, the FATF extended this rule to include cryptocurrency companies. In addition, in 2020, the G20 and a number of other jurisdictions began to include a travel rule in their local anti-money laundering laws.
The reasons why the travel rule is important are:
- The main purpose of this rule is to prevent the financing of terrorism and money laundering.
- It increases transparency in the cryptocurrency sector.
- Law enforcement agencies may receive transaction data by issuing subpoenas.
- The travel rule ensures that crypto firms follow sanctioned practices.
- This is the world’s first crypto law, and it could pave the way for more standard crypto regulation.
- The most significant effect of this rule will be the integration of the crypto market into the existing financial industry, allowing a more organized and mature asset class to emerge.
How to Implement AML Compliance?
In order to correctly implement the AML compliance, crypto firms should look for solutions that help automate these compliance processes.

- Onboarding and identity verification. Crypto transactions can take mere seconds to complete. That’s why there is increased pressure to get the on-boarding process right. To do everything the best way possible, crypto firms should consider using a layered approach to identity verification. For example, they may choose to conduct an examination of identity documents in addition to a video or photo KYC check. It is also important to consider slowing down the onboarding process. This can be done by instituting a mandatory 24-hour wait between onboarding and completing transactions.
- Screening and monitoring. After onboarding a customer, crypto firms should be able to monitor their customers for changes: if they have been added to sanctions or watch lists, if there are changes in their politically exposed person status, or if the status of any relatives and close associates notably changes. Crypto firms also should ensure they have the necessary tools to detect whether their customers have been involved in adverse media stories.
- Transaction monitoring. Like banks, crypto firms should monitor and understand the transactional behavior of their customers and scan them for anomalous and suspicious activity. However, the speed of transactions and the variety and volume of data transmitted with each transaction can make the scanning procedure quite challenging. Moreover, firms have to ensure that their transaction monitoring tools are tailored and calibrated to ensure proper scrutiny of transactions where cryptocurrencies are cashed out and converted to fiat currency. A proper segmentation of customers is crucial.
MiCA Regulation
The upcoming EU regulatory framework covers all crypto parties, including issuers of stablecoins, trading platforms, and digital wallets where crypto coins are held. The framework aims to protect investors and crypto issuers and defend the world’s financial stability while driving innovations and facilitating the adoption of crypto assets.
MiCA is expected to protect EU crypto consumers from a variety of risks linked to crypto investments and fraudsters. Nowadays, consumers have little or no protection at all, especially when EU citizens perform transactions outside of the EU. With these new rules in place, issuers of crypto assets and crypto-asset service providers will be obliged to follow instructions and protect the wallets of consumers. Under MiCA regulations, crypto issuers and service providers will be liable in cases involving the loss of crypto assets.
Moreover, MiCA requires all actors in the crypto-asset market to acknowledge the impacts of their climate and environmental footprints. The key actors, according to MiCA, include:
- Issuers of crypto assets
- Crypto-asset service providers
This legislative package sets up particular requirements for crypto actors, such as:
- Publish a whitepaper, a kind of tech manifesto
- Register with the EU authorities and obtain a license
- Meet minimum and ongoing capital requirements
- Comply with various organizational requirements
Once the framework enters into force, EU crypto players will be able to legally conduct their activities within all EU member states. To a certain degree, the MiCA regulation framework mirrors the existing MiFID framework.
What crypto asset services will be regulated under MiCA?
The law introduces challenging requirements for crypto players. However, the new rules won’t affect tokens without issuers like Bitcoin, but trading platforms will be obliged to warn their customers about the risks associated with trading. Here’s what MiCA regulates:
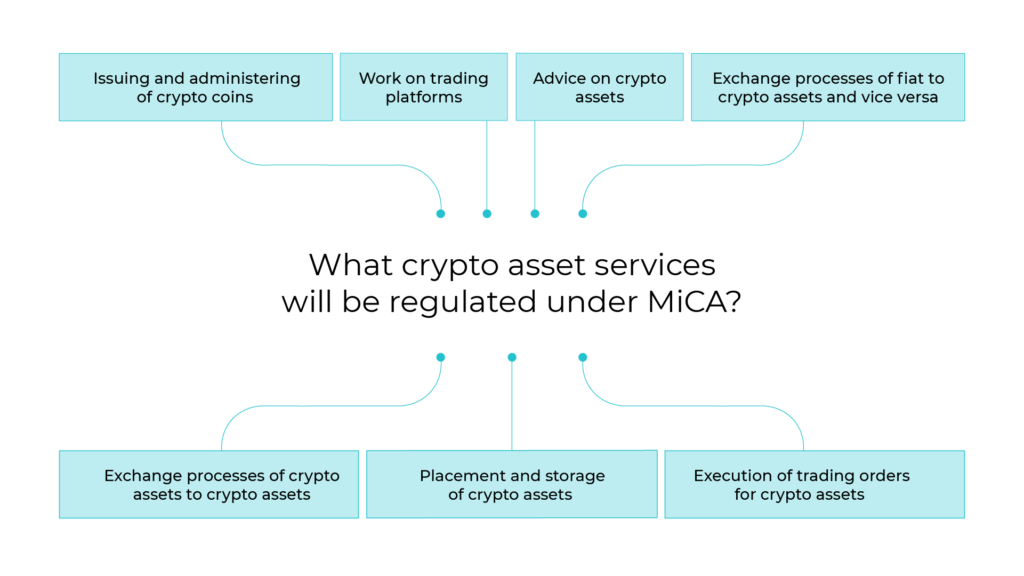
- Issuing and administering of crypto coins
- Work on trading platforms
- Exchange processes of fiat to crypto assets and vice versa
- Exchange processes of crypto assets to crypto assets
- Placement and storage of crypto assets
- Execution of trading orders for crypto assets
- Advice on crypto assets
Areas that MiCA doesn’t cover:
- Blockchain technology
- The process of crypto mining
- CBDCs (Central Bank Digital Currency)
- Security tokens and everything else regulated by MiFID II, EMoney Directive, and others.
- NFTs

How do AML/KYC Compliances Work?
Both procedures are carried out using special software. KYC software operates like gathering information to build a database. AML software uses various algorithms to link the KYC database (and other sources of information) to all wallet addresses on a blockchain. This is how an AML database is formed, which is constantly updated as cryptocurrency wallets and information about their owners are updated. Building, updating, and analyzing an AML database is a difficult task. This is because, in addition to the depth and number of links in the database, there is a different number of participants, which for simplicity, are grouped into so-called clusters. Each cluster is assigned a conditional risk of being involved in illegal activities as a percentage.
It is worth noting that although KYC and AML procedures are independent of each other, their tools can be used in parallel — an example being exchanges, most of which resort to using the KYC procedure. But instead of collecting tons of personal information to track financial flows and stop illegal activity, it is much more efficient to use AML tools that verify cryptocurrency addresses before transactions occur. So the user retains both their anonymity and the purity of their crypto assets as dubious funds are not able to make their way into users’ wallets. At the same time, illegal cryptocurrency remains at the disposal of the owner — to avoid transferring it and subsequently getting blocked on an exchange.
Emerging Use Cases and Threats for AML/KYC Compliances
Ransomware
Widespread digital adoption has led to a significant uptick in cybercrime risks, particularly ransomware attacks. They increased by 105% in 2021 compared to 2020, and regulators from the US, Asia Pacific and elsewhere have been exploring how to tighten controls and address this threat.
Sanctions Evasion
Russia’s war in Ukraine and the harsh sanctions issued by many Western countries in response has intensified discussions as to how nations and bad actors can exploit
crypto to evade sanctions. While officials say there is currently no evidence that designated Russian individuals or entities have used crypto to dodge sanctions in any material way, regulators are taking this possibility seriously. Crypto firms must ensure they take steps to detect and prevent this activity.
Terrorist Financing
Cryptocurrency assets and DeFi feature prominently in terrorist financing efforts. These currencies and technologies enable cross-border transactions with relative anonymity that
don’t involve an intermediary, settle in minutes and are often very difficult to stop or reverse once initiated. The fragmented regulatory landscape also increases the likelihood suspicious transactions will go undetected, particularly in pockets of the world with lax AML/CFT oversight.
Darknet Markets
These global online marketplaces enable buyers and sellers of illicit drugs, identity information and other illegal goods and services to communicate and transact. The threat that bad actors will exploit crypto firms to facilitate trade in these marketplaces is particularly acute since participants often use virtual currencies as their preferred method of payment.
Bitcoin is currently the most preferred cryptocurrency across the different darknet markets. However, monero has grown in popularity recently, and some signs indicate it may overtake bitcoin in the coming years.
Fraud
As cryptocurrencies become more widely used, cryptocurrency fraud will increase. Already fraud has proven to be a serious and growing threat: according to a recent report by Chainalysis, $14 billion flowed to addresses linked to criminals in 2021 — nearly double the amount directed to illicit addresses in 2020 ($7.8 billion). Notably, crimes involving scams and stolen funds experienced the most growth.
How to Implement AML/KYC Compliance without Investing Weeks and Thousands of Dollars
A complete AML/KYC solution comes with a hefty price tag. Annual subscription for a full-fledged and reliable AML/KYC service goes beyond 100 000 USD. At the same time, software that costs less is weak and usually won’t satisfy the necessary compliance requirements. Moreover, not all tools on the market have the functionality that the client requires.
In order to strike the perfect balance and help our customers succeed, Unicsoft develops our own AML/KYC compliance solutions, when boxed solutions from the market are not suitable for the project or are overpriced.
When developing crypto exchanges or other crypto platforms for our customers, it is often necessary to implement the compliance component. So we are ready to develop custom features covering specific product needs, like turnover count, user blocking logic, transaction processing, and thus save hugely on the compliance costs of the project. Our compliance solution allows our customers to be far ahead of their competitors who use boxed solutions from the market and have to stick to the limited functionality they offer.
Unicsoft provides unique AML features. Some of them are:
- Two types of registration: private and corporate accounts. For each type we develop different types of questionnaires to collect information.
- Account processing, considering each type.
- Real-time calculation of transaction turnover for the last year and comparison with the allowable limit.
- Collecting proof of address.
- Collecting proof of funds.
- Collecting information for tax reports.
This means that besides complying with AML/KYC itself, Unicsoft is ready to provide ready-to-use compliance solutions which are in no way inferior to individual software solutions. However, since Unicsoft provides AML/KYC compliance as part of an all-in-one solution, we’re able to dramatically drop the price and time to deployment. Contact us to learn more about.





![Guide 2023: AML/KYC Compliance Implementation in Crypto What’s the EU Artificial Intelligence Act and How to Comply? [Webinar]](https://unicsoft.com/wp-content/uploads/2024/03/Cover_1140_v1.1-370x280.png)

